Symmetry | Free Full-Text | Modified Advanced Encryption Standard Algorithm for Information Security

Table 1 from Enhancement of Advanced Encryption Standard (AES) Cryptographic Strength via Generation of Cipher Key-Dependent S-Box | Semantic Scholar

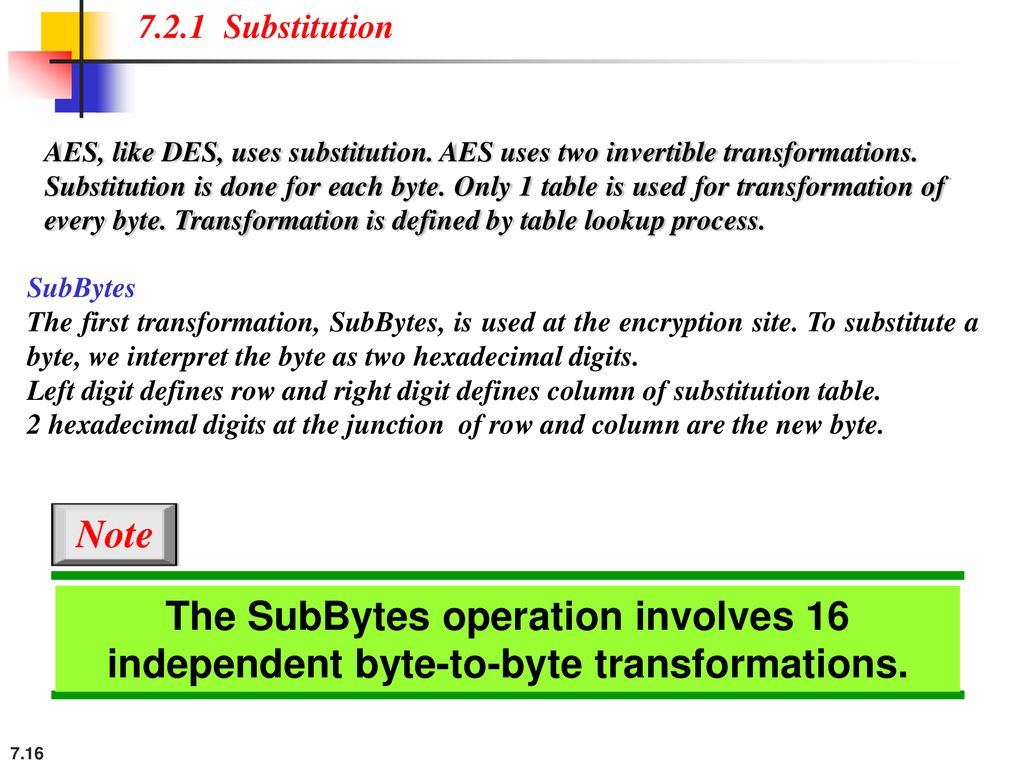
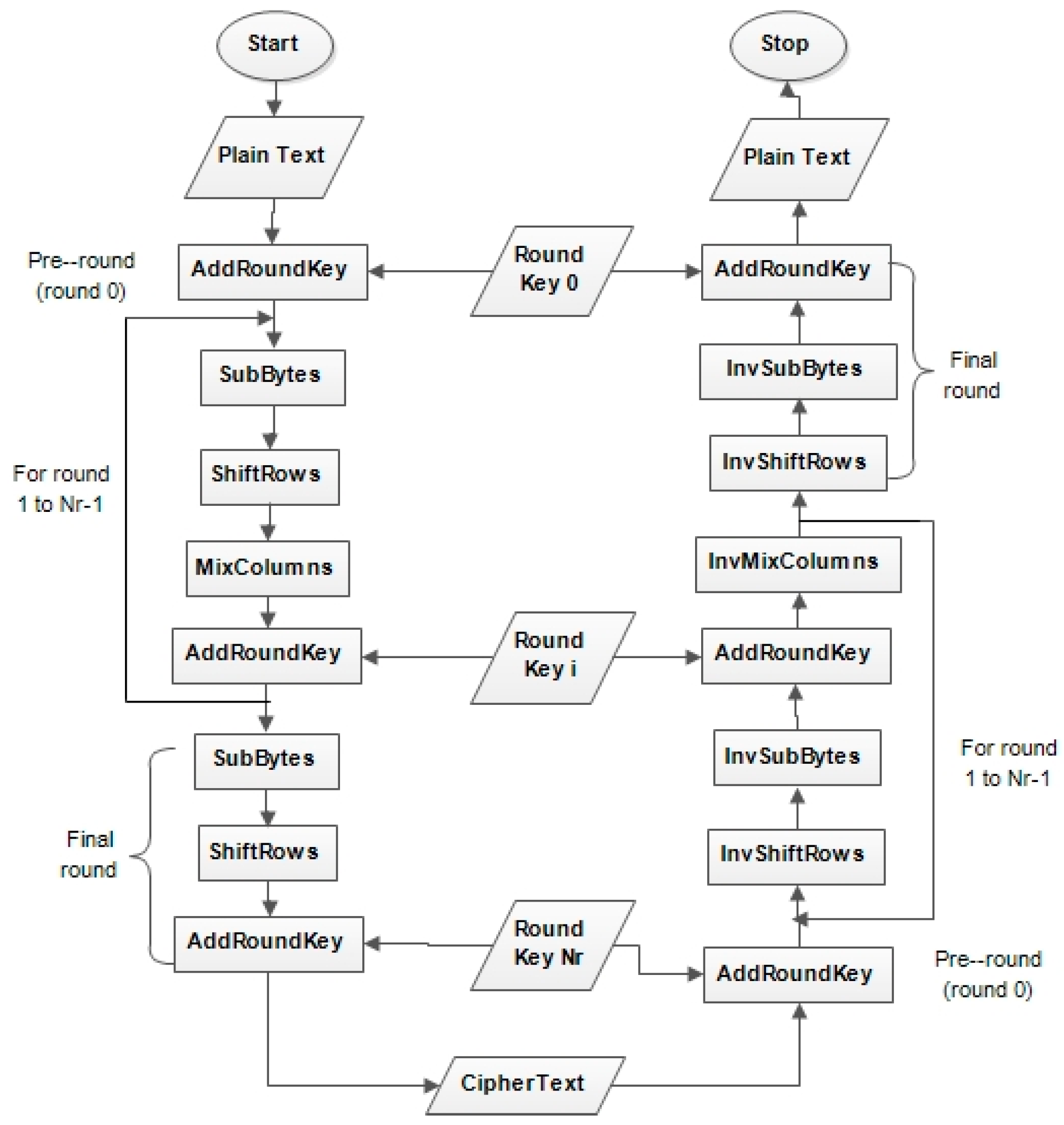
Information Security Lab. Dept. of Computer Engineering 122/151 PART I Symmetric Ciphers CHAPTER 5 Advanced Encryption Standard 5.1 Evaluation Criteria. - ppt download
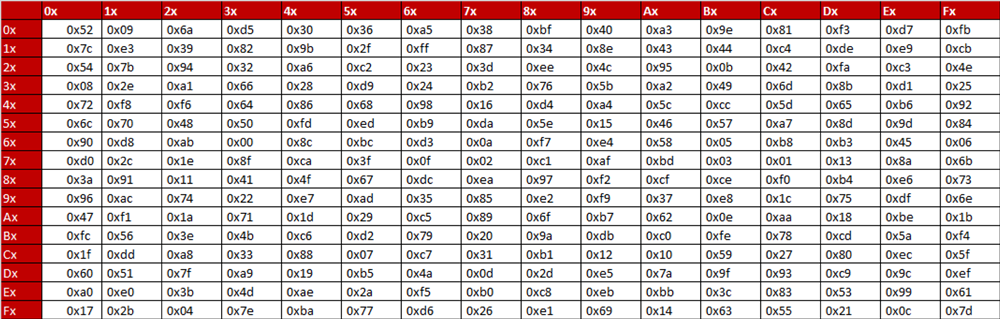
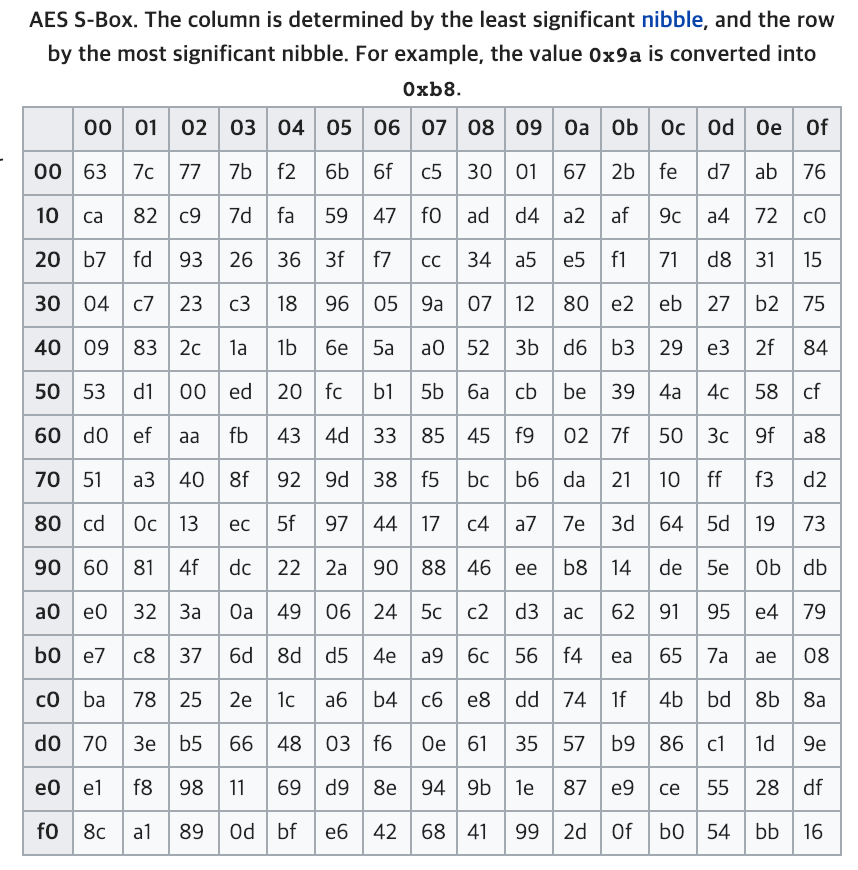
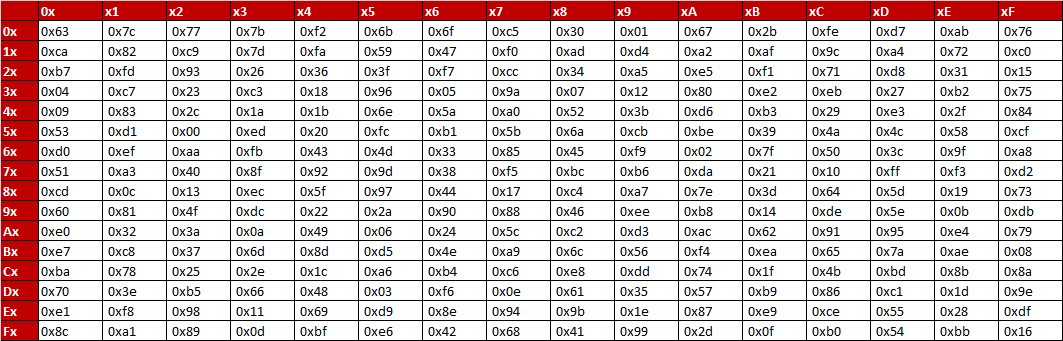
S-box table Substitution for each byte in the state array, for example... | Download Scientific Diagram

An In-Depth Guide To AES Encryption With Angular Service Implementation | by Israel Miles | Level Up Coding

Inverse S-box: substitution values for the byte xy (in hexadecimal format). | Download Scientific Diagram


![PDF] AN IMPROVED AES S-BOX AND ITS PERFORMANCE ANALYSIS | Semantic Scholar PDF] AN IMPROVED AES S-BOX AND ITS PERFORMANCE ANALYSIS | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/af65a349981b8c3ef96c1f7725ba78c398aba27b/7-Table3-1.png)