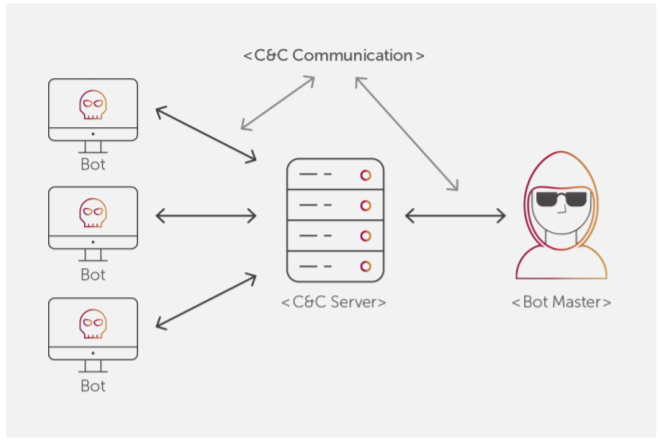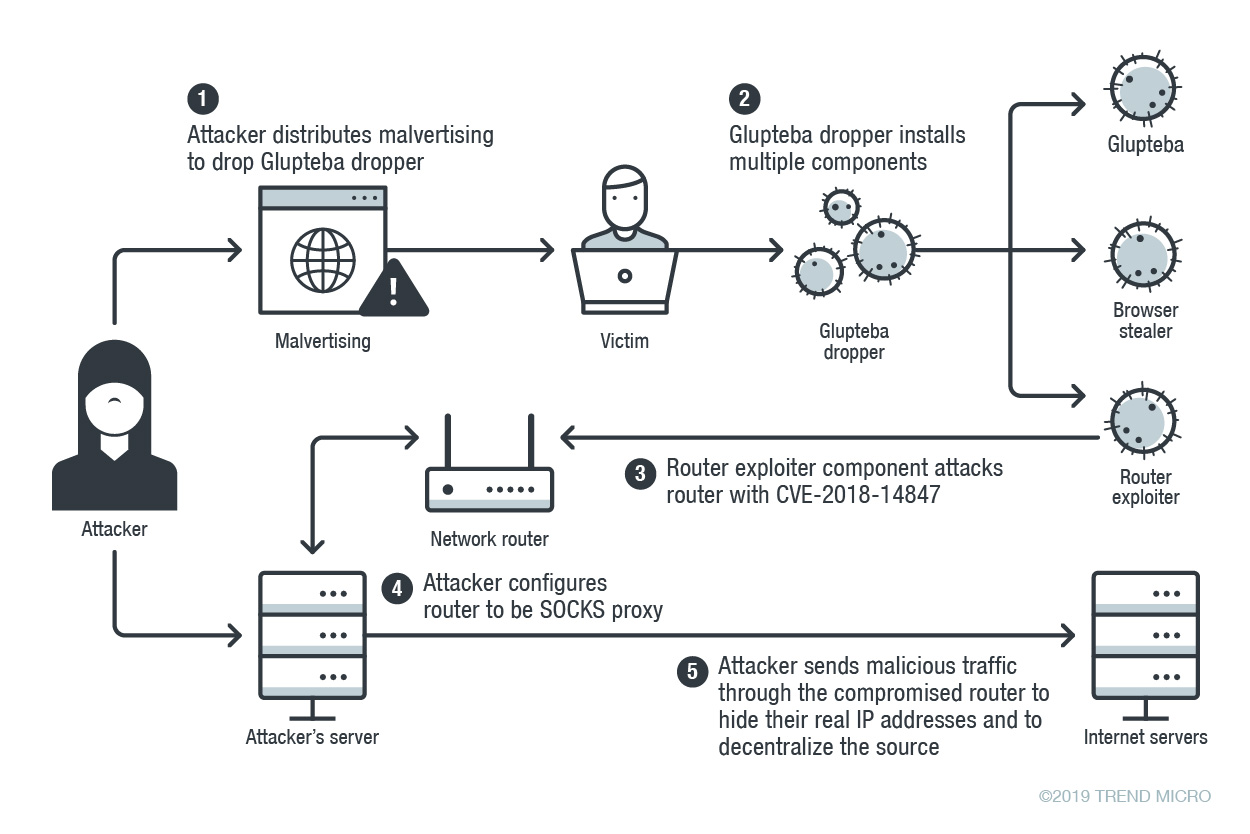
Glupteba Campaign Hits Network Routers and Updates C&C Servers with Data from Bitcoin Transactions - Malware Analysis - Malware Analysis, News and Indicators

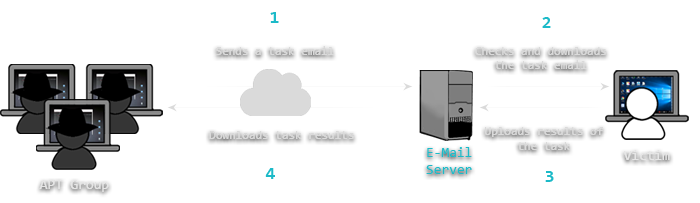
Malware hides C&C server communications using Google Docs function - Security AffairsSecurity Affairs

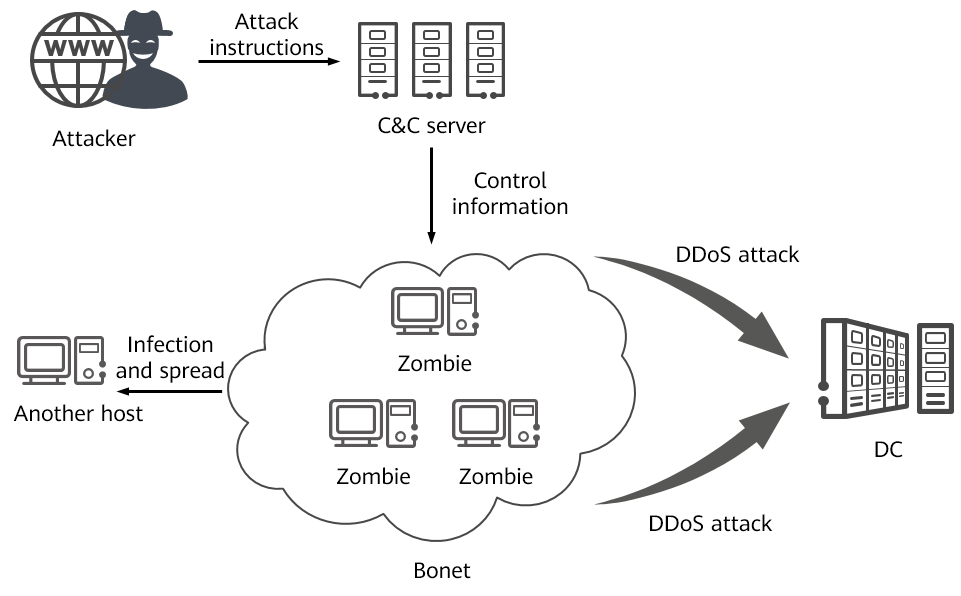
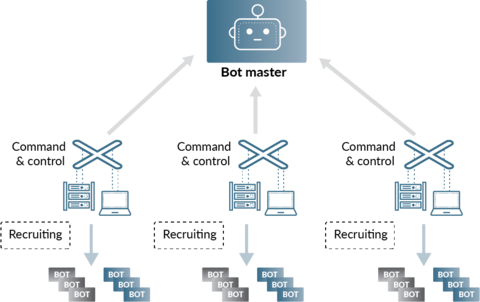
New Miori Malware Uses Text-based Protocol to Communicate with C&C Server for Launching a DDoS Attack | CyberCureME