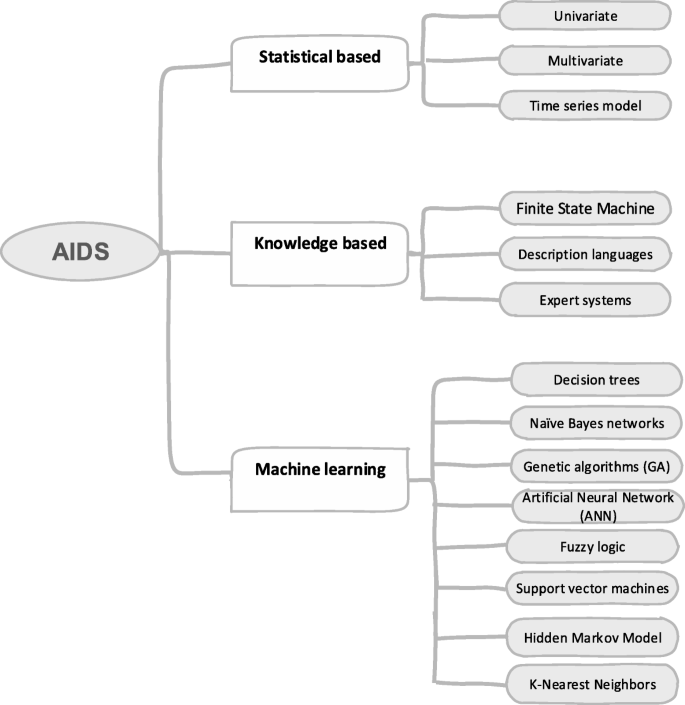
Survey of intrusion detection systems: techniques, datasets and challenges | Cybersecurity | Full Text

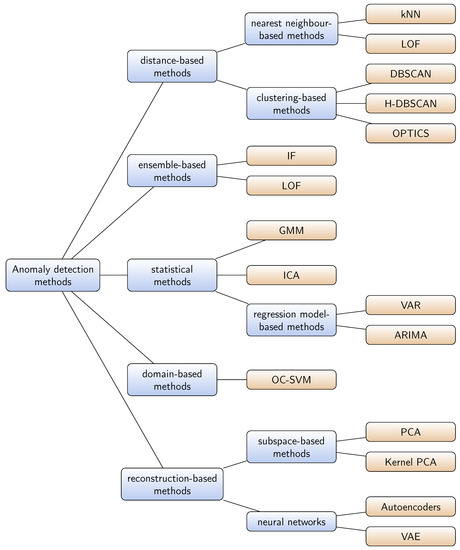
An improved density peaks clustering algorithm based on grid screening and mutual neighborhood degree for network anomaly detection | Scientific Reports

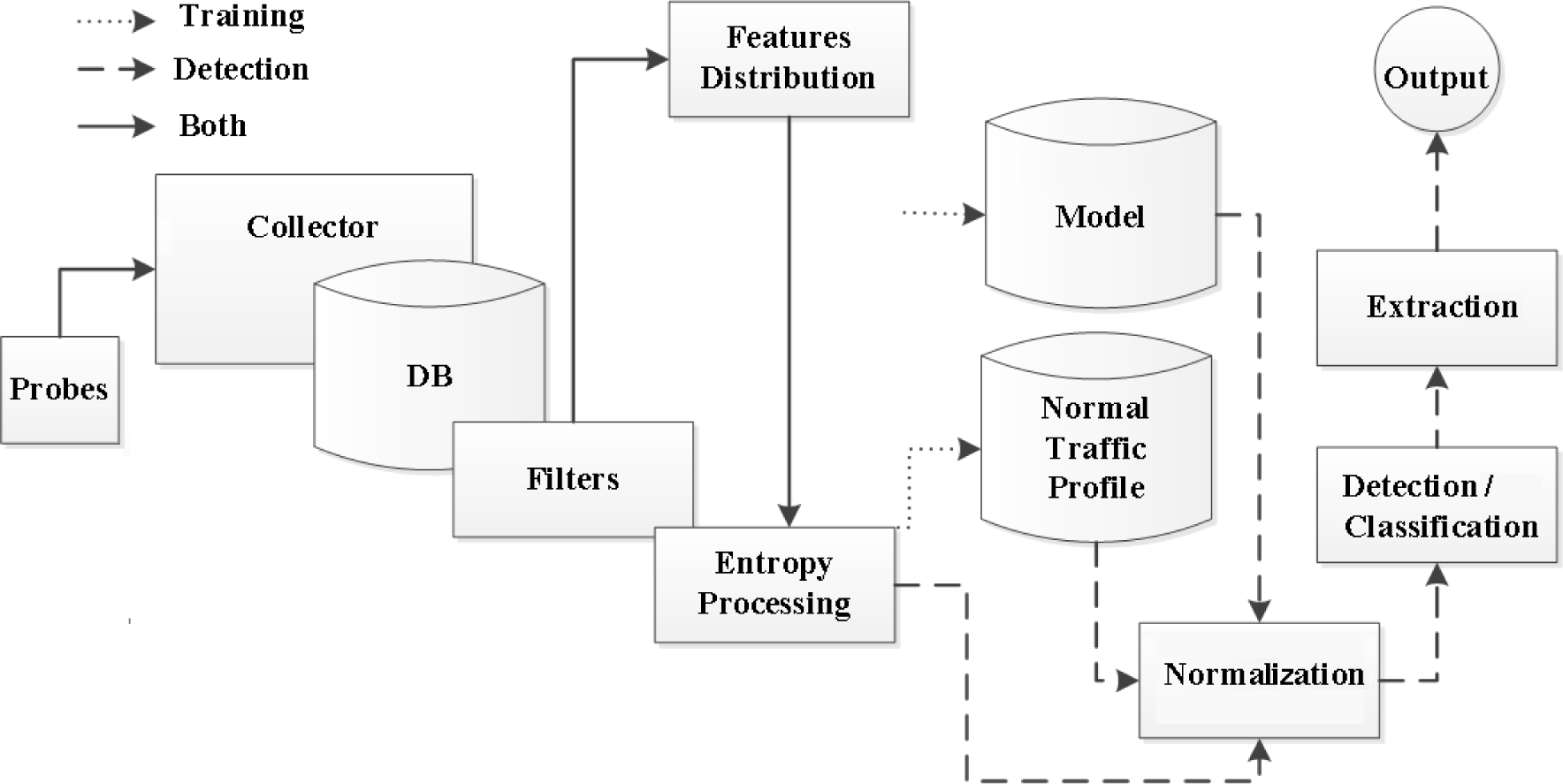
Network Anomaly Detection System. (Red arrows represent control actions... | Download Scientific Diagram
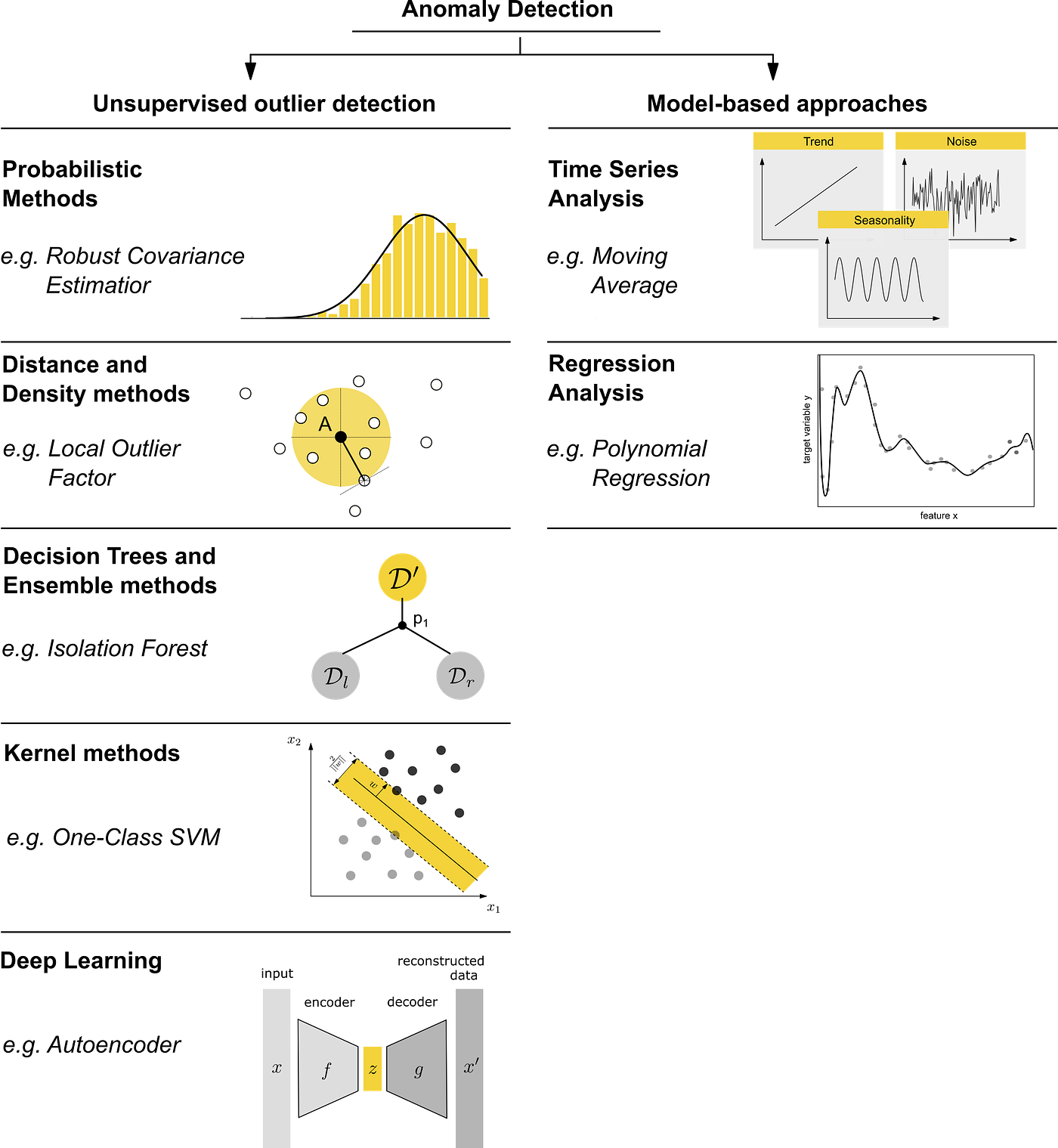
A Comprehensive Beginner's Guide to the Diverse Field of Anomaly Detection | by Dominik Polzer | Towards Data Science

Network intrusion detection system: A systematic study of machine learning and deep learning approaches - Ahmad - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/14-Figure10-1.png)

![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/20-Figure13-1.png)

![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/18-Figure12-1.png)


![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/7-Figure3-1.png)
![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/10-Figure6-1.png)


![PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar PDF] Network Anomaly Detection: Methods, Systems and Tools | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e467ff1ea3a0c535a0cef87f7e0daa414d524d9d/5-Figure1-1.png)
