Applied Sciences | Free Full-Text | Integration of Machine Learning-Based Attack Detectors into Defensive Exercises of a 5G Cyber Range | HTML
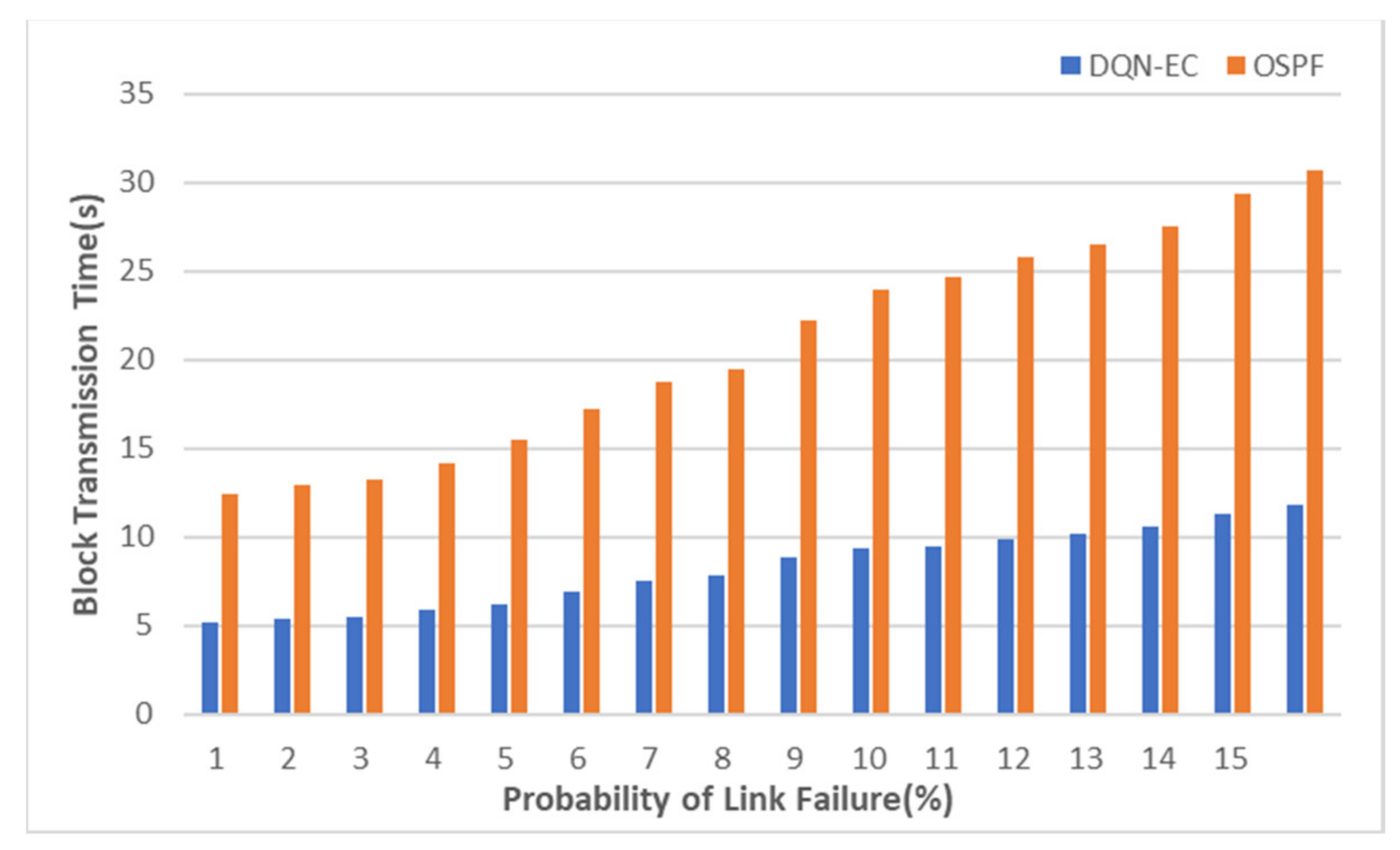
Applied Sciences | Free Full-Text | Deep Reinforcement Learning-Based Network Routing Technology for Data Recovery in Exa-Scale Cloud Distributed Clustering Systems | HTML
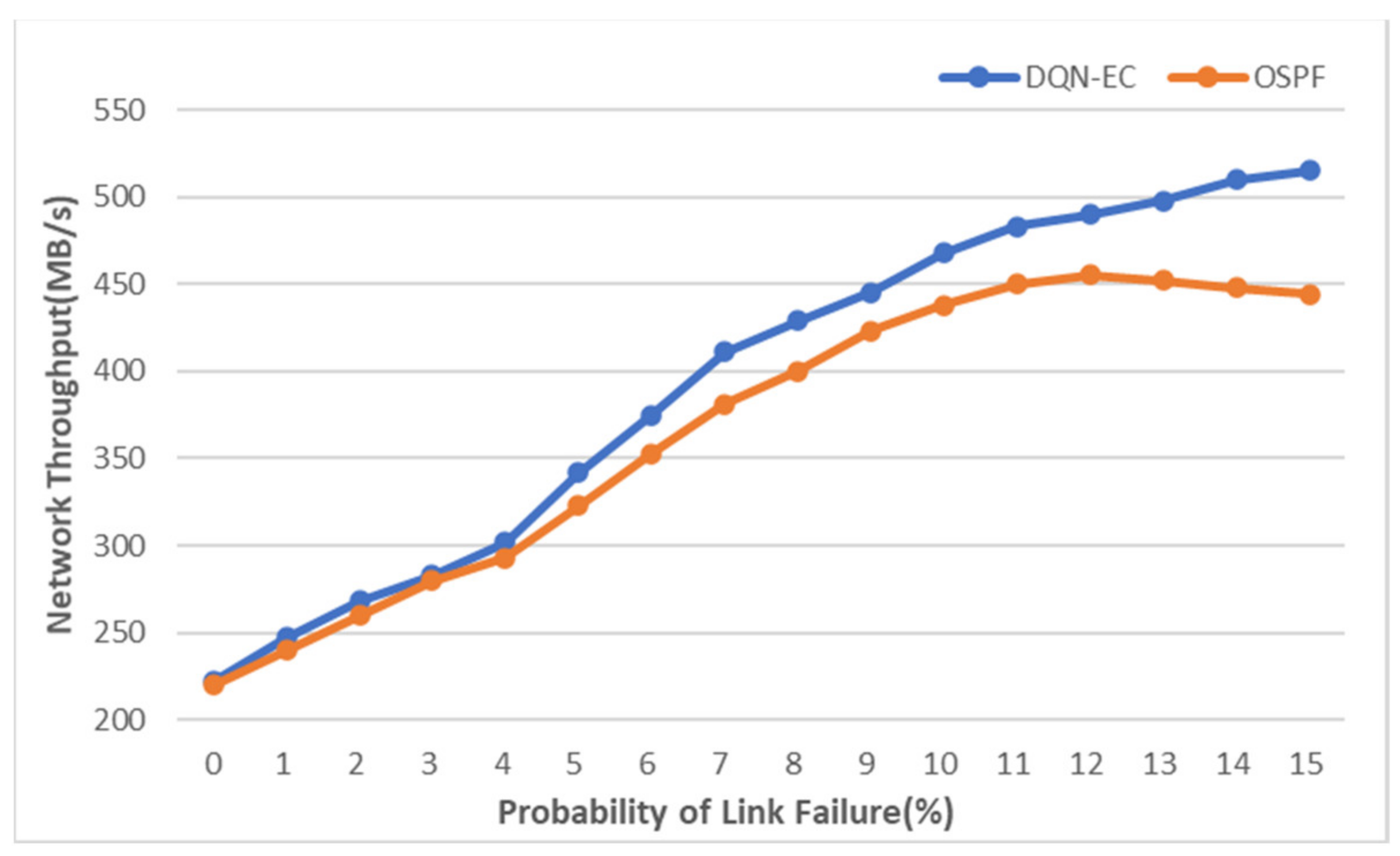
Applied Sciences | Free Full-Text | Deep Reinforcement Learning-Based Network Routing Technology for Data Recovery in Exa-Scale Cloud Distributed Clustering Systems | HTML

PDF) A combined hardware-software architecture for network flow analysis | Morris Sloman - Academia.edu
Denial of Service Attacks Prevention using Traffic Pattern Recognition over Software-Defined Network